The CWE Top 25 list reflects the most serious software security weaknesses. I invite you to read the updated top list to become aware of the changes happened over the past year.
We position the PVS‑Studio analyzer not only as a tool for searching bugs in code but also as a tool for static application security testing (SAST) tool. For a better understanding of trends and planning of diagnostic rules, there is nothing better than to look at the latest list of the most relevant security issues. There are several such lists, for example, OWASP Top 10, SANS Top 25, and the above-mentioned CWE Top 25.
By the way, last year we already wrote about changes in the CWE Top 25 2021 — you can find the article here.
To better understand the context, let's brush up on some topics. To do this, let's skim through the following points:
If you feel CWE savvy, you can safely skip this section. Otherwise, I strongly recommend that you refresh those points before you read the article. Below is a rather free interpretation of some questions from CWE FAQ and CVE FAQ:
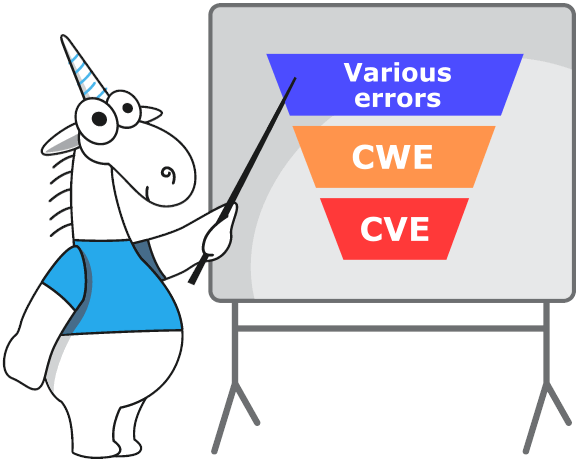
How does a software weakness differ from a software vulnerability?
Weaknesses are defects, failures and other issues of implementation, design or architecture of the software that may lead to vulnerabilities.
Vulnerabilities are errors that have already been found by someone. Attackers may exploit these vulnerabilities to get access to a system or a network, to disrupt services, etc.
What is CWE and how is it different from CVE? How does CVSS figure here and where did KEV come from?
Why do I need to know about CWE?
Today, developers use CWE as the main tool when discussing the elimination and/or minimizing security defects in the architecture, design, code, and software implementation. Organizations use CWE as a standard measure for evaluating software security verification tools and as a common baseline standard for identifying, preventing, and minimizing negative consequences.
What is CWE Top 25?
CWE Top 25 is a list of the most dangerous and common defects. These defects are dangerous because someone can easily find and exploit them. Attackers can use them to disrupt the application's operation, steal data or even completely take over a system. CWE Top 25 is a significant community resource that can help you get an idea of the currently most common and dangerous security defects.
What is an algorithm to compile and rank the CWE Top 25 list?
The main sources for this year's list were:
The CWE team researches handled the obtained data according to the View-1003 method to reduce the specificity of records. For example, CWE-122 (Heap-Based Buffer Overflow) is converted to basic CWE-787 (Out-of-Bounds Write). The CWE team also filtered the data and removed from the Top 25 list the following items:
Next, the team of researchers used their own formula to calculate the ranking order. This formula takes into account the potential danger of exploit and the frequency, with which a defect (CWE) is the main cause of a vulnerability. The team made the formula that way, so it normalizes the frequency and predicted severity relative to their minimum and maximum values. To obtain the frequency of mentions, the formula calculates how many times CVE referred to CWE within the NVD.
Freq = {count(CWE_X' ∈ NVD) for each CWE_X' in NVD}
Fr(CWE_X) = (count(CWE_X ∈ NVD) - min(Freq)) / (max(Freq) - min(Freq))
Another important component of the scoring formula is a defect's severity. The following formula calculates it:
Sv(CWE_X) = (average_CVSS_for_CWE_X - min(CVSS)) / (max(CVSS) - min(CVSS))
At the end, the final score is calculated by multiplying the frequency of mention by the severity score.
Score(CWE_X) = Fr(CWE_X) * Sv(CWE_X) * 100
In general, the methodology of data analysis has not changed much this year. But next year, the CWE team is planning more significant changes. Here are some of them:
You can find more information about the methodology of data preparation and analysis in the supplemental details pertaining to the CWE Top 25 list.
How big is the sampling this year?
The dataset contained a total of 37,899 CVEs from the previous two calendar years.
Is the Top 25 updated every year?
Yes, it is updated annually. For information about previous versions, visit CWE Top 25 archive.
Who participates in the development of CWE Top 25?
The CWE community includes individual researchers and representatives of numerous organizations, the scientific community, and government agencies. They are all interested in elimination of software defects. You can get a list of CWE Team members on the "CWE Community Members" page.
Read more about classification on the cwe.mitre.org website.
Below is a table of correspondence between the CWE Top 25 2022 list and the PVS-Studio diagnostic rules, divided by programming languages. You can always check the most up-to-date table with CWE Top 25 coverage on our website.
|
# |
CWE ID |
Name |
Score |
KEV |
PVS‑Studio diagnostics |
|---|---|---|---|---|---|
|
1 |
Out-of-bounds Write |
64.20 |
62 |
C#: V3106 Java: V6025 |
|
|
2 |
Improper Neutralization of Input During Web Page Generation ('Cross-site Scripting') |
45.97 |
2 |
C#: V5610 |
|
|
3 |
Improper Neutralization of Special Elements used in an SQL Command ('SQL Injection') |
22,11 |
7 |
C#: V5608 |
|
|
4 |
Improper Input Validation |
20,63 |
20 |
||
|
5 |
Out-of-bounds Read |
17,67 |
1 |
C#: V3106 Java: V6025 |
|
|
6 |
Improper Neutralization of Special Elements used in an OS Command ('OS Command Injection') |
17.53 |
32 |
C#: V5616 |
|
|
7 |
Use After Free |
15.50 |
28 |
||
|
8 |
Improper Limitation of a Pathname to a Restricted Directory ('Path Traversal') |
14.08 |
19 |
C#: V5609 |
|
|
9 |
Cross-Site Request Forgery (CSRF) |
11.53 |
1 |
Coming in the future |
|
|
10 |
Unrestricted Upload of File with Dangerous Type |
9,56 |
6 |
Coming in the future |
|
|
11 |
NULL Pointer Dereference |
7,15 |
0 |
C++: V522, V595, V664, V713, V1004 C#: V3027, V3042, V3080, V3095, V3100, V3125, V3145, V3146, V3148, V3149, V3152, V3153, V3168 |
|
|
12 |
Deserialization of Untrusted Data |
6.68 |
7 |
C#: V5611 |
|
|
13 |
Integer Overflow or Wraparound |
6,53 |
2 |
C++: V629, V658, V673, V683, V1026, V1028, V1083, V1085, V5004, V5005, V5006, V5007, V5010, V5011 C#: V3113 Java: V6105 |
|
|
14 |
Improper Authentication |
6.35 |
4 |
Coming in the future |
|
|
15 |
Use of Hard-coded Credentials |
5.66 |
0 |
C++: V5013 C#: V5601 Java: V5305 |
|
|
16 |
Missing Authorization |
5,53 |
1 |
Coming in the future |
|
|
17 |
Improper Neutralization of Special Elements used in a Command ('Command Injection') |
5.42 |
5 |
C#: V5616 |
|
|
18 |
Missing Authentication for Critical Function |
5.15 |
6 |
Coming in the future |
|
|
19 |
Improper Restriction of Operations within the Bounds of a Memory Buffer |
8.85 |
6 |
||
|
20 |
Incorrect Default Permissions |
4.84 |
0 |
Coming in the future |
|
|
21 |
Server-Side Request Forgery (SSRF) |
4.27 |
8 |
C#: V5618 |
|
|
22 |
Concurrent Execution using Shared Resource with Improper Synchronization ('Race Condition') |
3.57 |
6 |
Coming in the future |
|
|
23 |
Uncontrolled Resource Consumption |
3.56 |
2 |
Coming in the future |
|
|
24 |
Improper Restriction of XML External Entity Reference |
3.38 |
0 |
C#: V5614 |
|
|
25 |
Improper Control of Generation of Code ('Code Injection') |
3.32 |
4 |
C++: V1076 |
The table shows that the PVS-Studio static analyzer now covers 68% (17 out of 25) the CWE Top 25 2022 list. Last year, the coverage was 52%. Significant improvement in coverage over the year is a credit to the large number of SAST-oriented diagnostic rules that were released by PVS-Studio over the past year.
The biggest upshifts:
|
# |
CWE ID |
Name |
Position in 2021 |
Position in 2022 |
Annual change |
|---|---|---|---|---|---|
|
1 |
Concurrent Execution using Shared Resource with Improper Synchronization ('Race Condition') |
33 |
22 |
11▲ |
|
|
2 |
Improper Neutralization of Special Elements used in a Command ('Command Injection') |
25 |
17 |
8▲ |
|
|
3 |
Uncontrolled Resource Consumption |
27 |
23 |
4▲ |
|
|
4 |
NULL Pointer Dereference |
15 |
11 |
4▲ |
|
|
5 |
Improper Control of Generation of Code ('Code Injection') |
28 |
25 |
3▲ |
The biggest downshifts:
|
# |
CWE ID |
Name |
Position in 2021 |
Position in 2022 |
Annual change |
|---|---|---|---|---|---|
|
1 |
Insufficiently Protected Credentials |
21 |
38 |
17▼ |
|
|
2 |
Exposure of Sensitive Information to an Unauthorized Actor |
20 |
33 |
13▼ |
|
|
3 |
Incorrect Permission Assignment for Critical Resource |
22 |
30 |
8▼ |
|
|
4 |
Missing Authentication for Critical Function |
11 |
18 |
7▼ |
"Newbies" in the Top 25:
|
# |
CWE ID |
Name |
Position in 2021 |
Position in 2022 |
Annual change |
|---|---|---|---|---|---|
|
1 |
Concurrent Execution using Shared Resource with Improper Synchronization ('Race Condition') |
33 |
22 |
11▲ |
|
|
2 |
Uncontrolled Resource Consumption |
27 |
23 |
4▲ |
|
|
3 |
Improper Control of Generation of Code ('Code Injection') |
28 |
25 |
3▲ |
And in the end — the defects that were dropped out of the CWE Top 25 in 2022:
|
# |
CWE ID |
Name |
Position in 2021 |
Position in 2022 |
Annual change |
|---|---|---|---|---|---|
|
1 |
Exposure of Sensitive Information to an Unauthorized Actor |
20 |
33 |
13▼ |
|
|
2 |
Insufficiently Protected Credentials |
21 |
23 |
2▼ |
|
|
3 |
Incorrect Permission Assignment for Critical Resource |
22 |
30 |
8▼ |
Key points:
As a bonus, let's see what defects did not make it into the 2022 CWE Top 25 and may well enter the top next year:
|
# |
CWE ID |
Name |
Score |
KEV |
Annual change |
|---|---|---|---|---|---|
|
26 |
Improper Certificate Validation |
3.12 |
2 |
- |
|
|
27 |
Uncontrolled Search Path Element |
3.12 |
0 |
7▲ |
|
|
28 |
Incorrect Authorization |
3.10 |
0 |
10▲ |
|
|
29 |
Improper Privilege Management |
3.06 |
3 |
- |
|
|
30 |
Incorrect Permission Assignment for Critical Resource |
2.93 |
1 |
8▼ |
|
|
31 |
Access of Resource Using Incompatible Type ('Type Confusion') |
2.87 |
10 |
5▲ |
|
|
32 |
Exposure of Resource to Wrong Sphere |
2.68 |
0 |
21▲ |
|
|
33 |
Exposure of Sensitive Information to an Unauthorized Actor |
2.49 |
2 |
13▼ |
|
|
34 |
Improperly Controlled Modification of Object Prototype Attributes ('Prototype Pollution') |
2.48 |
0 |
new |
|
|
35 |
URL Redirection to Untrusted Site ('Open Redirect') |
2.41 |
0 |
2▲ |
|
|
36 |
Missing Release of Memory after Effective Lifetime |
2.39 |
0 |
4▼ |
|
|
37 |
Improper Link Resolution Before File Access ('Link Following') |
2.38 |
4 |
6▼ |
|
|
38 |
Insufficiently Protected Credentials |
2.25 |
0 |
17▼ |
|
|
39 |
Cleartext Transmission of Sensitive Information |
2.15 |
0 |
4▼ |
|
|
40 |
Cleartext Storage of Sensitive Information |
2.01 |
0 |
1▲ |
Although these defects did not make it to the top, they are still important because under favorable circumstances they may turn into vulnerabilities.
I hope you enjoyed this article and understood the current terminology.
Fortunately, static analyzers help us fight potential vulnerabilities. Therefore, I invite you to download and test the PVS-Studio static analyzer on your project. Maybe a couple of CWEs crept into your code and are about to become CVE :)
0