Static code analysis is a method used to detect flaws, errors, and potential vulnerabilities in the source code. Static analysis is considered an automated code review process.
Code review is one of the oldest and most effective methods of defect detection. The process involves developers who attentively read the source code and give recommendations for improving it. While reading the code, programmers detect errors, or code fragments that can become errors in future. It is also considered that the code author should not explain how different parts of the program work. The reviewer should understand the program's execution algorithm from its text and comments. If the code is incomprehensible, it must be improved.
Usually, code review works well, since programmers notice someone else's errors much more easily. You can learn more about the code review method in Steve McConnell's wonderful book "Code Complete".
The only major disadvantage of the code review method is an extremely high price. You need to regularly gather several programmers to review new code or re-review the code after applying recommended changes. The programmers also need to rest regularly. If you try reviewing large code fragments at once, your attention is quickly blunted, and the code review benefits fade away.
So, you want to regularly review the code, but it's too expensive. A compromise solution is to use static code analysis tools. They tirelessly analyze the source code and give the programmer recommendations to pay special attention to certain code fragments. Of course, this kind of software will never replace a proper code review performed by a team of programmers. However, the benefit/price ratio makes static analysis a handy practice used by many companies.
Implementing static code analysis, you will get:
There are other ways to use static code analysis tools. For example, static analysis is used to control and train new employees, who are not yet familiar enough with the company's coding standards.
There are a lot of commercial and free static code analyzers. The Wikipedia website provides a large list of static analyzers: List of tools for static code analysis. Such tools support quite a lot of languages (C, C++, C#, Java, Ada, Fortran, Perl, Ruby, etc.).
If you wonder how code analyzers detect errors, check out the following example: PVS-Studio: static code analysis technology.
Like any other error detection method, static analysis has its strengths and weaknesses. It is important to understand that there is no ideal testing method. Different types of software and methods will give different results. You can achieve high software quality only by using both of these methods.
The main advantage of static analysis is the possibility to significantly reduce the cost of eliminating software's defects. The earlier the error is detected, the lower is the cost of fixing it. Thus, according to McConnell's "Code Complete", fixing an error at the testing stage will cost ten times more than at the construction (coding) stage:
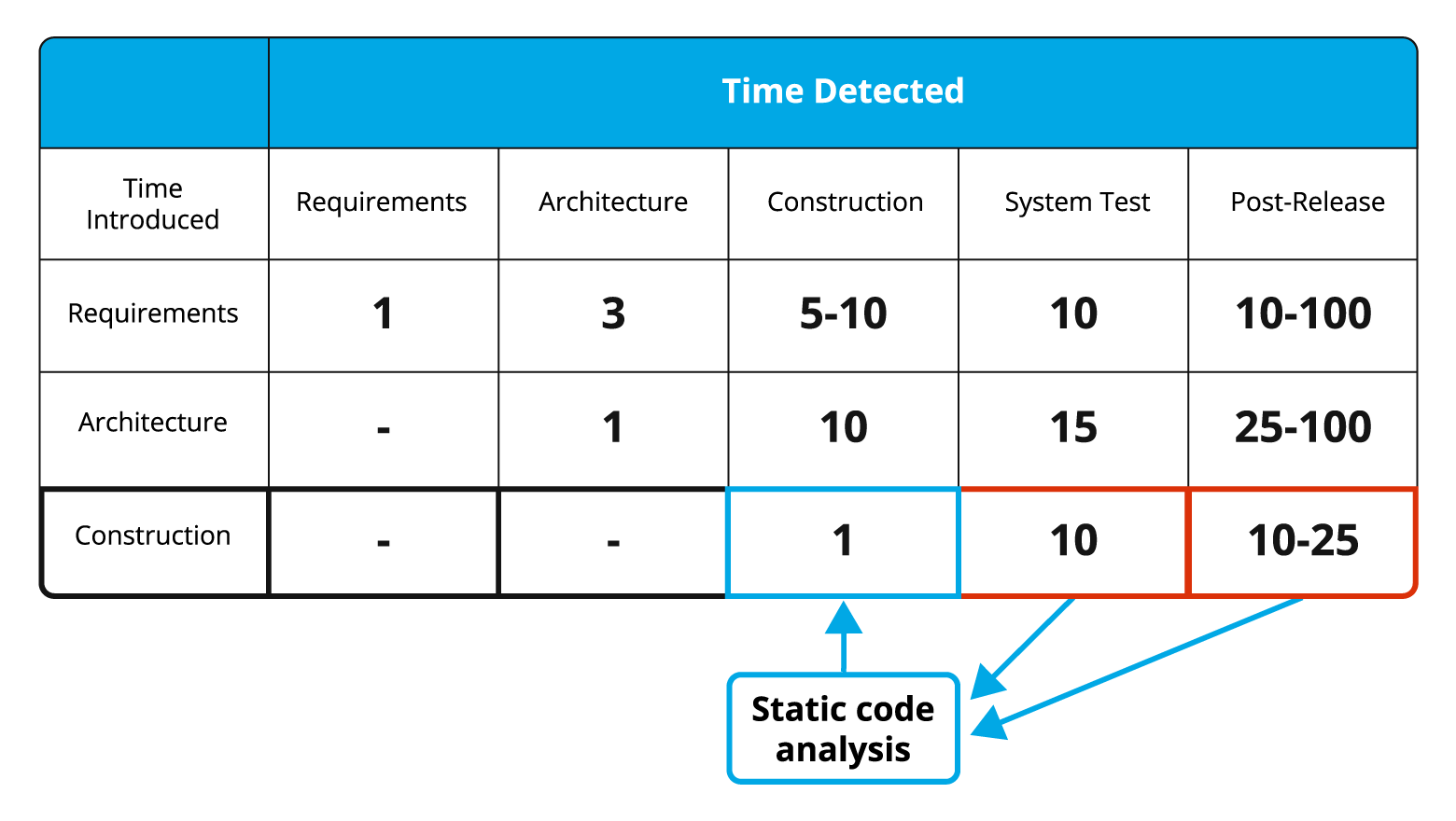
Figure 1. The average cost of fixing defects depending on the time they have been made and detected (the data are taken from the book "Code Complete" by S. McConnell).
Static analysis tools allow you to identify numerous errors at the coding stage, which significantly reduces the overall project development cost. For example, the PVS-Studio static code analyzer can run in the background immediately after compilation is done and notify the programmer if a potential error is found (see incremental analysis mode).
There are other advantages of static code analysis:
Errors detected by static analyzers are rather diverse. For example, here is the list of diagnostics implemented in the PVS-Studio tool. Some analyzers focus on a certain area, or certain types of defects. Others support certain coding standards, such as MISRA-C:1998, MISRA-C:2004, Sutter-Alexandrescu Rules, Meyers-Klaus Rules, etc.
Static Application Security Testing (SAST) is a form of static analysis. These analyzers are focused on identifying potential vulnerabilities in order to protect application code from zero-day vulnerabilities. In other words, the development team must find and fix security defects at the coding stage, so that attackers could not use them later for their malicious purposes.
The PVS-Studio analyzer is also a SAST solution.
The static analysis field is actively developing, new tools and new coding standards are emerging. Static analyzers implement new diagnostic rules, and some rules become obsolete. Different analyzers integrate into different IDEs, CI tools, cloud CI tools, and so on.
As a result, there is no way to comprehensively compare static analyzers and choose the "best" one. When you google something about static analyzers, you get just some overview articles which are not enough to make a decision. Therefore, it is reasonable to choose and try several tools which meet your requirements: language support, integration into CI/CD, IDE plugins, supported coding standards, etc. And then select the most suitable one that found real bugs in your project.
The next step is to introduce the tool into your development process. There are two excellent articles covering this topic:
0