In this article, you are going to learn about new useful features appeared in PVS-Studio over the past three years. The article contains several sections — so, you don't have to read the whole article, you can just choose a topic that is interesting for you.
PVS-Studio is a static analyzer that searches for errors and security defects in C, C++, C#, and Java code. The tool helps find issues in earlier stages of the development life cycle — when it's easier and cheaper to fix them. As a result, developers spend less time debugging, and managers save money.
You can find more information on the product page.
Below we discuss the main enhancements added from the beginning of 2020 to the end of 2022. You can choose any topic you are interested in to find more details.
General
You can use PVS-Studio plugins in lots of IDEs: Visual Studio, Visual Studio Code, Rider, CLion, IntelliJ IDEA, Qt Creator.
The "Best Warnings" filter simplifies your first experience. The mechanism allows you to easily sort the analyzer warnings. With just one click (literally), you get warnings that most likely indicate an error. There are only 10 filtered warnings, so you can view them quickly.
Analyzers for all supported languages (C, C++, C#, Java) work on Windows, Linux, and macOS. For now, only the CLI version of C++ analyzer works under Apple ARM (via Rosetta).
The C++ analyzer can run intermodular analysis — this helps find more issues. C# has similar feature too.
The analyzer also provides the mode to check the list of files. This helps check commits, pull requests, and merge requests.
The PVS-Studio results can be converted into new formats: TeamCity, SARIF, GitLab, MISRA Compliance.
The analyzer handles code written in C++20, C# 11, and Java 11. It also supports earlier versions of languages.
At the time of writing the article, PVS-Studio has more than 1,000 diagnostic rules that identify various issues in code.
Security
The OWASP Top 10 2021 list of web application security risks is fully covered: there is at least one PVS-Studio diagnostic rule for each category.
PVS-Studio diagnostics are mapped according to CWE, OWASP ASVS, and SEI CERT Coding Standards.
The C# analyzer performs software composition analysis (SCA).
Embedded
PVS-Studio provides diagnostics that detect deviations from safety coding standards by MISRA and AUTOSAR.
In the Wrap Compilers mode, the CLMonitor and C and C++ Compiler Monitoring UI utilities intercept all compilers' invocations. Previously, utilities could not analyze part of code if the compilation process finished quickly.
The analyzer works with a large number of compilers for embedded systems: IAR ARM, MPLAB XC8, QNX, C6000-CGT.
GameDev
PVS-Studio handles projects based on Unreal Engine 4 and Unreal Engine 5.
The analyzer has a better understanding of Unreal Engine- and Unity-specific types.
In Unreal Engine projects, you can use baselining and more analyzer settings. All these features are also available for Unity.
One of the main directions of the analyzer development is the search for security defects. PVS-Studio gets new mechanisms (for example, taint analysis) which help find more potential vulnerabilities in the code. The analyzer's diagnostic rules are mapped according to CWE, SEI CERT and OWASP ASVS — this simplifies the work with the analysis results for cyber security specialists.

PVS-Studio covers all categories of the most critical security threats — OWASP Top 10 2021. This means that for each category of the list there's at least one diagnostic rule that finds the corresponding issues. Which ones? SQL injections, XSS, outdated cryptographic algorithms, hardcoded passwords in source code, etc.
PVS-Studio users working with C# projects can now search for project dependencies on vulnerable components. To do this, PVS-Studio performs software composition analysis (SCA): it finds which components application uses and searches for known vulnerabilities among them.
Useful links:
Compliance tables of PVS-Studio diagnostics with the list of potential vulnerabilities and secure development standards:
Among all security defects there are the most dangerous and common ones. You can learn more about how PVS-Studio helps fight them here:
Another direction of the analyzer's development is code checking for embedded systems. There are several aspects here: the support for safety development standards (MISRA, AUTOSAR), and toolchains used in embedded development.
Compilers
In the embedded development world, there are many different compilers that the analyzer must support. Code support for new compilers allows more developers to use the analyzer. This is one of the areas in which we work. For example, PVS-Studio now understands the code for the following compilers: IAR ARM, MPLAB XC8, QNX, C6000-CGT.
You can find the full list of supported compilers on the product page (the "Supported languages and compilers" section).
Support for safety development standards
The cost of errors in the code for embedded systems is high. To reduce the chance of an error, there are coding standards. Following their recommendations, developers can write code that is easier to read and maintain. This code is less error-prone and more safe.
We added several dozens of special diagnostic rules to PVS-Studio to search for deviations from safety development standards. Here are the links to view what deviations from rules of safety development the analyzer diagnostics are looking for:
When working with MISRA standards, you may need a MISRA Compliance report. If you need more information, read the following article explaining how to get the report.
Improved compiler monitoring system
An important enhancement that I'd like to mention concerns the CLMonitor and C and C++ Compiler Monitoring UI utilities. They check C and C++ projects on Windows regardless of the build system. To collect the necessary information, the analyzer intercepts compilers' invocations.
The utilities had a drawback mostly noticeable when developing software for embedded systems. If the code was compiled quickly, the lifetime of the process was short. That's why the system could miss compiler calls, and as a result, not all the project code was analyzed.
If you have encountered similar issues before, I recommend trying the new mode — Wrap Compilers. It intercepts all compilers' invocations regardless of how fast the code is compiled. This means that there should be no problems with the fact that not all the code is analyzed.
Errors in the GameDev industry are not as critical as in the embedded systems industry, but they can still be costly. That's why static analysis is also useful in GameDev.
We enhance PVS-Studio integration with two game engines: Unreal Engine and Unity.
Unity
PVS-Studio handles Unity projects in the same way as other C# projects — in the same environment (the command line, Visual Studio, Rider) with a full set of functions — you can hide warnings on legacy code, suppress false warnings, etc.
As for Unity, we focus on understanding Unity-specific types: how methods behave, Unity-style null checks, etc. This helps find more possible errors and issue fewer false positive warnings.
Here's the documentation explaining how to run Unity projects analysis with PVS-Studio.
Unreal Engine
Unreal Engine projects use their own build system — Unreal Build Tool. That's why some analyzer functions available for Visual C++ projects were previously not available for UE projects (for example, disabling warnings on legacy code).
We are constantly improving integration with Unreal Engine projects. Here are the most significant enhancements:
Here's the documentation explaining how to run Unreal Engine projects analysis with PVS-Studio.
Diagnostic rules
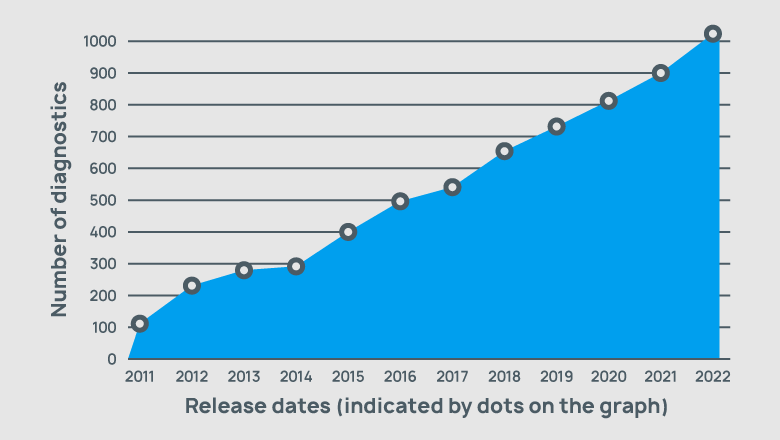
Over 3 years, about 300 diagnostic rules have been added to PVS-Studio, and their total number now exceeds 1,000.
Here's what diagnostics search for in the code:
The full list of diagnostics is available here.
The most interesting warnings of the analyzer
Running the analyzer on a project for the first time, you can get a large number of warnings. It may take you a while to view them all. So, is there a way to view the warnings that most likely indicate an error? Yes. PVS-Studio provides a special mechanism called "Best Warnings". This is a filter that chooses the most interesting warnings among all. There are no more than 10 warnings — so you can quickly view them.
You can find more information about this filter in the following note: "PVS-Studio: 2 features for a quick start".
Supported coding standards
Here are coding standards and platforms that PVS-Studio supports:
PVS-Studio also works with earlier versions of programming languages.
Cross-platform integration
Now analyzers for all languages (C, C++, C#, Java) work on 3 main platforms: Windows, Linux, and macOS.
Java and C# analyzers, as well as plugins for Rider, CLion, and IntelliJ IDEA cannot yet be used on Apple ARM processors (M1, M2, etc.). Now we are collecting user feedback to understand the demand for this. So, if you'd like PVS-Studio to support these processors — let us know.
Integration with IDE
We are striving to make PVS-Studio available in different environments. One of the directions is the development of plugins for IDEs. Now you can use PVS-Studio plugins for the following IDEs:
Here's the documentation explaining how to use the analyzer in each of the listed IDEs.
Analysis of commits, pull requests, and merge requests
It's better to run project analysis regularly. However, developers often need to check only part of the code. For example, when working in the IDE, a developer changed several files. In this case, it makes sense to check not the entire project, but only the modified files. That's why PVS-Studio provides the incremental analysis mode. It helps run analysis faster, and developers don't have to view warnings for code that is unfamiliar for them.
Sometimes developers have another task — check the modified code within CI. This is relevant for checking commits, pull requests, and merge requests. Previously, the analyzer didn't provide such feature. We added it in one of the earliest releases. You can find the information on how to set up this type of analysis in the documentation.
Intermodular analysis
In the intermodular analysis mode, PVS-Studio considers the information not only from the analyzed translation unit but also from the related ones. Such analysis is much deeper and allows to find more issues in the code.
In the C# analyzer, intermodular analysis is enabled by default. In the C++ analyzer, this mode is disabled by default. To enable it, you need to set the appropriate value of the "Intermodular Analysis Cpp" option.
Report formats for other tools
PVS-Studio analysis results can be converted into formats used in other tools. So, you check the code using PVS-Studio, convert the results into a format for TeamCity, and then work with them (you can also work with them in this CI system).
New supported formats are TeamCity, SARIF, GitLab, MISRA Compliance. To view a complete list of formats, read the documentation on how to view and convert analyzer's results.
You can find the full history of changes on the release history page. If you want to be up-to-date on what's new in the analyzer, you can subscribe to our newsletter.
Have you found this article inspiring? Why don't you try the analyzer? Don't hesitate and download it from this page.
0