PVS-Studio 7.26 has been released. Now you can run the analysis in plugins for VS Code and Qt Creator; upload the analysis results to DefectDojo, and more. In this note, we'll take a closer look at these and other enhancements.
You can download the latest version of PVS‑Studio here.
Visual Studio Code and Qt Creator: running analysis and suppressing warnings
Now the PVS-Studio plugins for Visual Studio Code and Qt Creator support the analysis of C and C++ projects. Moreover, the plugins support mass suppression of analyzer warnings (with the help of suppress files). This mechanism enables you to hide warnings for legacy code and work only with new warnings. In this way, the integration of the analyzer into the project will be much easier. You can read more about it in the article: "How to introduce a static code analyzer in a legacy project and not to discourage the team".
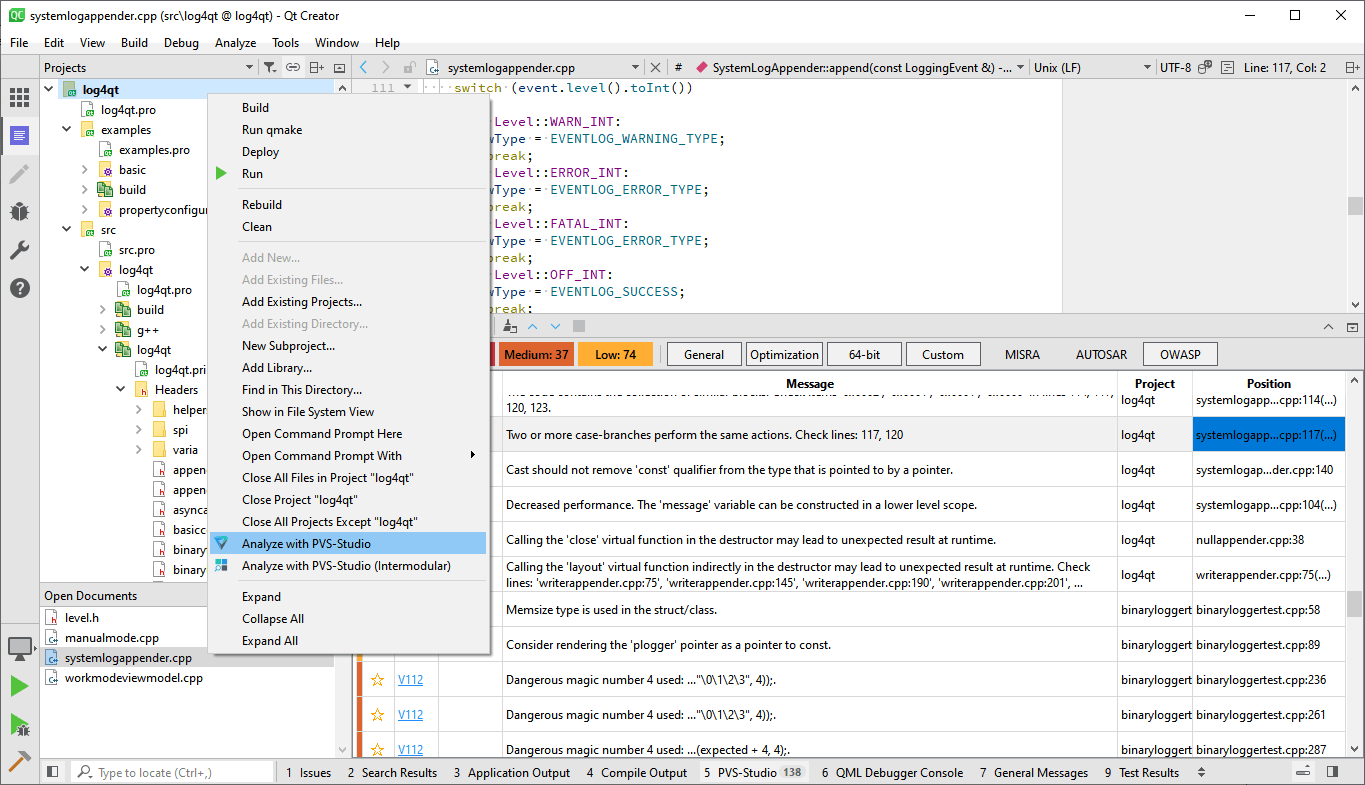
Now you can analyze the projects that use the following build systems:
You can find more detailed information in the documentation:
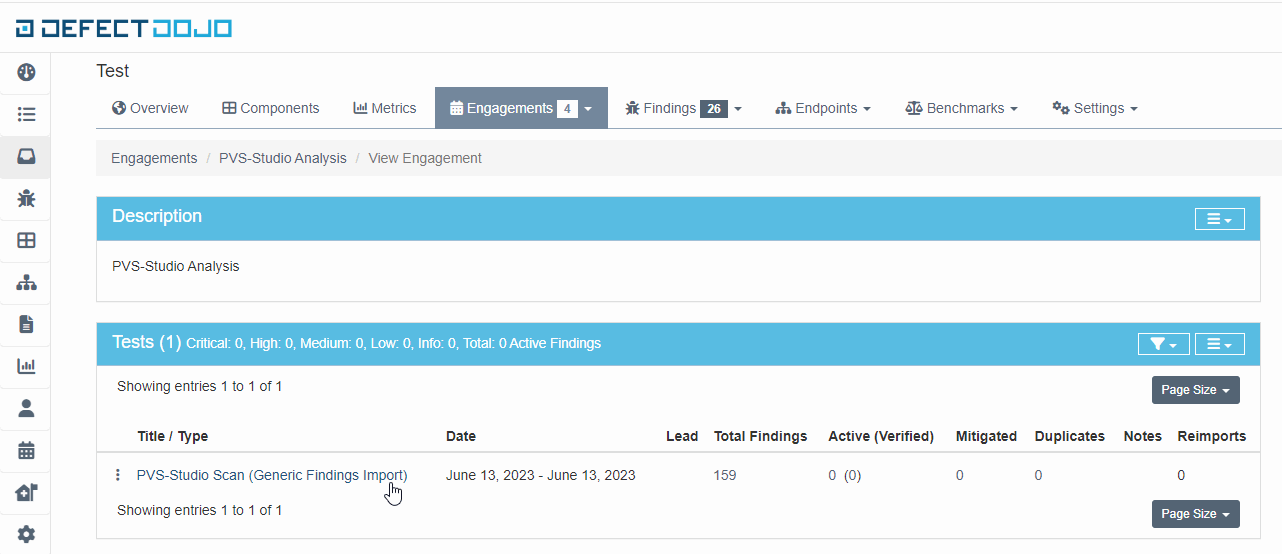
Integration with DefectDojo
Now PVS-Studio has integration with DefectDojo, the DevSecOps platform that helps teams manage the entire security workflow. Find out more details in the documentation.
Support for JDK 20 projects
The Java analyzer now supports projects that use JDK 20 and Java 20. It also maintains backward compatibility with all previous versions.
New features for C and C++ function annotations
Function annotations give PVS-Studio more data for analysis.
The C++ analyzer received an enhanced user annotation mechanism. Now you can write annotations for functions at any nesting level. Moreover, now it's possible to use the function name without specifying the class and namespace when annotating.
Here you can find the guidelines for user annotations.
New diagnostics
C++
C#
Articles
For those who code in C#:
For those who code in C++:
For more articles, you can visit our blog.
**
Do you need to check a project with PVS-Studio? Then start from this page.
0