I'm currently studying a report by PVS-Studio analyzer with the results of a fresh check of the Chromium project and the libraries it employs. Based on these results, I'm going to write a series of articles discussing some types of bugs and ways to avoid them. But there was one bug that I liked so much that I decided to tell you about it right off in this small blog post.
Our team already posted 5 articles (1, 2, 3, 4, 5) about the search of bugs in open-source project Chromium, and it seems there'll be a few more soon.
I'm currently studying a fresh report by PVS-Studio and just noting down the warnings to use later when writing the posts, which is the next step. I prefer to look through the report first and only then decide which of the defects and in what form to describe. But one bug was especially nice, so I decided to tell you about it right off.
This error is found in the Protocol Buffers (protobuf) library used by Chromium. Protocol Buffers is a protocol for serializing structured data developed by Google as a smaller and faster binary alternative to the XML text format.
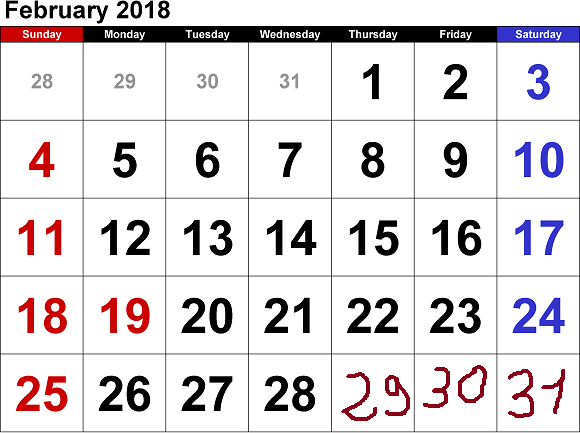
If I had come across that bug a couple of months ago, I'd have paid it no attention. It's just an ordinary bug like many others. But when I saw it the other day, I immediately recalled the recent epic failure of cash registers in Russia. On December 20, the major retailers and gas-station chains all over Russia were faced with a glitch in the new model of cash registers. The first to suffer was Vladivostok; then it spread across the country as the new day was breaking and affected Novosibirsk, Barnaul, Krasnoyarsk, Kemerovo, and other large cities.
The bug in the cash registers and the bug in Protocol Buffers are different bugs that are not linked in any way. But I wanted to show you how errors of this type occur. After all, defects often stem from banal typos rather than tricky algorithms. I don't know what exactly was wrong with the code of the cash registers, but I do know how a silly typo breaks the ValidateDateTime function used for date validation in the Protocol Buffers library. Let's look into the code of the function.
static const int kDaysInMonth[13] = {
0, 31, 28, 31, 30, 31, 30, 31, 31, 30, 31, 30, 31
};
bool ValidateDateTime(const DateTime& time) {
if (time.year < 1 || time.year > 9999 ||
time.month < 1 || time.month > 12 ||
time.day < 1 || time.day > 31 ||
time.hour < 0 || time.hour > 23 ||
time.minute < 0 || time.minute > 59 ||
time.second < 0 || time.second > 59) {
return false;
}
if (time.month == 2 && IsLeapYear(time.year)) {
return time.month <= kDaysInMonth[time.month] + 1;
} else {
return time.month <= kDaysInMonth[time.month];
}
}ValidateDateTime receives a date as an argument and must find out if that date is correct or not. Basic checks are performed first and involve checking that the date components are within the corresponding ranges: [1..12] for the month, [1..31] for the day, [0..59] for the minutes, and so on. The code is clear enough and we don't need to go into it.
This is followed by a more complicated check where the function checks if the given day exists in the given month. For example, December consists of 31 days, while there is no such date as November 31-st as there are only 30 days in that month.
To check the validity of the day value without using multiple if statements or a long switch, the programmer used a helper array called kDaysInMonth, which stores the number of days in every month. The function refers to this array and looks up the maximum number of days in the given month and checks the given day value against it.
It also takes into account whether the year is a leap year, in which case February has one extra day.
So, the function is all neat and nice. Yet faulty.
Its code contains a typo that makes the check of the day value incorrect. If you look closely, you'll notice that what is compared with the maximum number of days in the month is the month value, not day value, from the date passed to the function.
Here it is again:
if (time.month == 2 && IsLeapYear(time.year)) {
return time.month <= kDaysInMonth[time.month] + 1;
} else {
return time.month <= kDaysInMonth[time.month];
}What should be used in the comparison "time.month <=" is the structure member day, not month. It means the correct version should look like this:
if (time.month == 2 && IsLeapYear(time.year)) {
return time.day <= kDaysInMonth[time.month] + 1;
} else {
return time.day <= kDaysInMonth[time.month];
}The month value (1 through 12) is, of course, always less than the number of days in any month.
Because of that, such dates as February 31 or November 31 will be treated as correct.
Nice bug, isn't it? It could make processing of incorrect dates possible, which in theory could be used for hacker attacks. Well, perhaps I'm exaggerating a bit, but that's what vulnerabilities usually look like: some input data goes unchecked and someone happens to be smart enough to exploit that.
This error (two errors, to be precise) is detected by the following PVS-Studio diagnostics:
As you can see, PVS-Studio now identifies programming issues according to Common Weakness Enumeration (CWE) as well.
Another thing I'd like to point out is that PVS-Studio is learning to analyze code at an even deeper level. The V547 diagnostic as such is an old-timer (it dates back to 2010), but it wouldn't have found this bug, say, a year ago. Now the analyzer can look into the array and notice that values within the range [28..31] are extracted. Besides, it understands that the value 0 shouldn't be taken into account in the array since the range of time.month is [1..12]. If the month value were 100, for example, the function would return - and the analyzer can figure that.
As a result, it sees that the following comparisons of ranges take place:
The conditions are therefore always true, and this is what the analyzer warns us about. That's how deep we can reach now. So, we not only add new diagnostics to PVS-Studio but also improve the Data-Flow analysis, which boosts the quality of the existing diagnostics.
Why is the range [2, 2] presented only with the number 2? The fact of the matter is that the specifying condition time.month == 2 is taken into account.
Now, the following question arises: "How can we improve our style to ward off errors like that?"
I have no answer to that. The function we've discussed is simple and well-written. It's just that human is prone to errors, and it's natural for us to make typos like that every now and then. Even experienced programmers aren't safe from that.
The only piece of advice I could give is to be especially careful when writing unit tests and use professional static code analyzers such as PVS-Studio.
Thank you for reading. And I'll go on with the report.
Update
The bug was fixed and new tests were added just one hour after we posted the article.
0