Security. What does this word mean to you? Nowadays, companies spare no effort to ensure that their product is secured from hacking and all sorts of information leaks. PVS-Studio decided to help its users and expand the functionality in this area. Therefore, one of the main innovations of the upcoming release will be the introduction of analyzer new features which will ensure code safety and security. This article aims to present these features.

At the moment, PVS-Studio is developing not only as a static analyzer searching for code quality defects (quality control solution) but also as a solution for searching for security and safety defects. In security context, the PVS-Studio analyzer is a SAST tool. SAST (Static Application Security Testing) is a type of static code analysis aimed at finding potential security vulnerabilities. Such an analysis can reveal a large number of flaws, including even those that haven't revealed themselves yet. Safety is another area focused on ensuring the reliability and fault tolerance of programs.
As the title of the article suggests, we are expanding the PVS-Studio functionality in these areas. Previously, there were various mapping tables of compliance with safety and security standards on our site. However, it was inconvenient because this information did not get directly into the analyzer report. Now we are making these analyzer features more user-friendly (for example, by integrating our IDE plugins into interfaces). What is more, we are expanding the existing database by supporting new standards. PVS-Studio was mentioned in the report Static Application Security Testing, Q3 2020 by Forrester Research, one of the leading researchers of the impact of new and innovative technologies on business processes and the market. That fact gave us an additional impetus to improve the analyzer features. You can read more about this and how we have developed as a SAST and safety solution here.
Well, to waste no time, let's point out the additions right away. So, here is what's new, safe, and cool in PVS-Studio:
Note. Previous versions have already supported security standards such as MISRA C:2012 and MISRA C++:2008. At the time of writing, 74 diagnostic rules have been implemented for them.
We also support the compliance of our diagnostics with the most common classification of potential vulnerabilities – CWE (Common Weakness Enumeration). We already have 514 diagnostics that fit this classification.
Let's talk a little bit about the new diagnostic groups (OWASP and AUTOSAR), which we previously had only on our site in the form of comparisons. The new release of PVS-Studio 7.12 includes diagnostics from these standards in separate groups of rules with their own numbers, documentation, and all the other things inherent in our diagnostic rules. That is, when checking a project, the analyzer issues warnings for new groups, as with other warnings. Previously, out of all the security and safety rules, only PVS-Studio diagnostics had separate groups that met the MISRA C and C++ standards.
Actually, what's the meaning of these unusual words: OWASP, AUTOSAR? Let's clarify the situation a bit.
The AUTOSAR C++14 Coding Guidelines is a set of guidelines for writing code in C++14. The set is used to work in systems where security and fault tolerance are important. This document is mainly used in the automotive industry. However, it can also be used in other industries dealing with the development of embedded systems.
For this standard, we created a separate group with numbers from 3500 to 3999. You can view the comparison of these diagnostics with the AUTOSAR standard here.
The OWASP Application Security Verification Standard is a list of application security requirements and tests that can be used by software architects, developers, testers, application security specialists, vendors, and users of tools for developing, building, testing, and verifying secure applications.
As you understand, unlike the AUTOSAR organization standard, OWASP ASVS is not tied to any particular language. That is why, we've implemented diagnostics of this type in all the languages we analyze (C, C++, C#, Java). These diagnostic rules received their own group and numbers from 5000 to 5999.
Now let's move on to CERT. The SEI CERT Coding Standard is a set of software writing standards for improving the reliability and security of software in C, C++, Java, and Perl. These standards are developed by the CERT Coordination Center (CERT/CC). You can find their comparison with the rules of PVS-Studio here.
However, in the case of CERT, we did not create a new group of diagnostics, because a significant part of our General Analysis falls under this standard. But don't worry. You will definitely find out that the diagnosis is a specific CERT rule. It is added to the analyzer report in the same way as OWASP ASVS or AUTOSAR C++14 Coding Guidelines.
At the same time, we continue to support standards such as MISRA C:2012 and MISRA C++:2008. These are software development standards. Their main purpose is to improve the security, portability, and reliability of programs for embedded systems (mapping).
By the way, we don't want to stop there. Our team will make more and more new diagnostics aimed at finding safety and security errors. PVS-Studio Roadmap 2021 also includes our plans for 2021.
Well, we've added new diagnostics. Are you curious to see the result? You'll definitely find it in our plugins! To date, we display information about security standards in plugins for three IDEs. These are Visual Studio (for versions from 2010 to 2019), JetBrains Rider, and IntelliJ IDEA. In order for the plugins to display these new warnings, the following improvements were made:
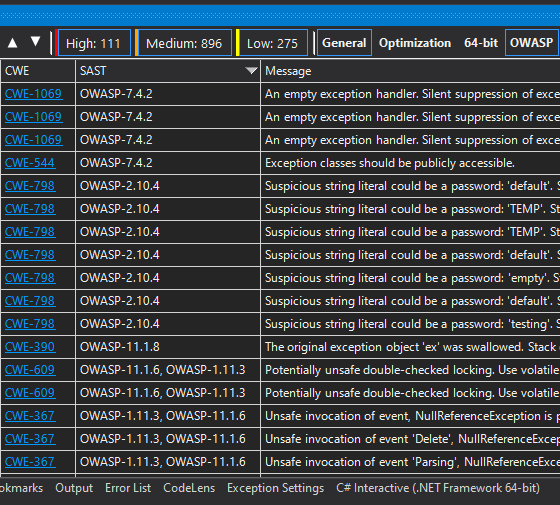
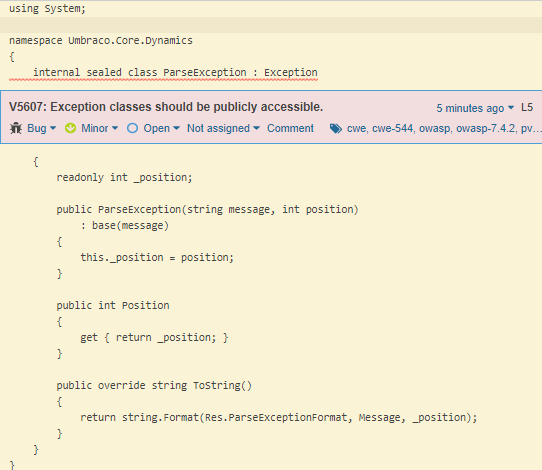
Here are a couple of pictures to give you an idea of what it looks like. In the plugin for Visual Studio 2019, it looks as follows:
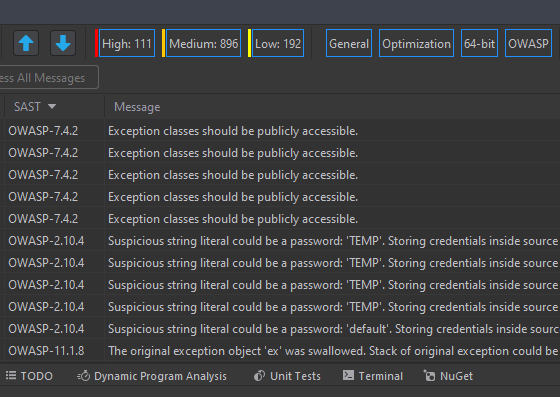
We added the same functionality in Rider and in IntelliJ IDEA. This is what it looks like in Rider:
We haven't forgotten our utility that helps to convert reports to various formats. Now all of our report types, in which the reports can be converted, support OWASP and AUTOSAR. Let's take FullHtml, perhaps, the most commonly used conversion type, as an example. This type allows you to view the report in a browser. It's nice and convenient if you can't work directly with the plugin in your development environment. Plus, it's easy to send such a report or a link to it by mail.
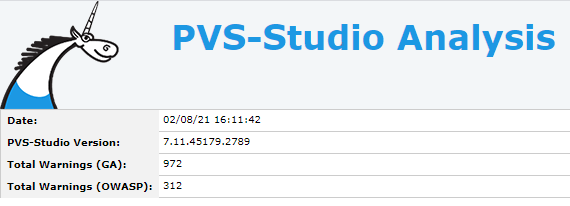
Actually, we quickly got the desired file. So, let's take a look at it. As you can see, there's a new Total Warnings (OWASP) field in the header. It indicates the number of potential errors from this category:
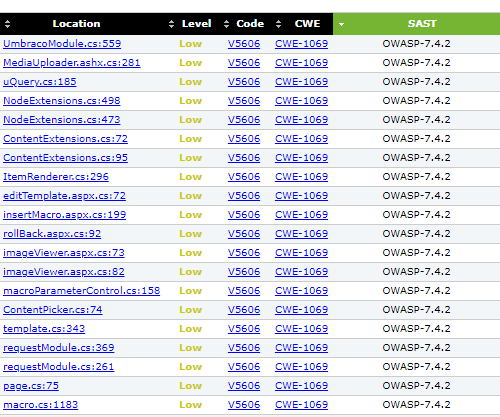
This is how the SAST column itself is displayed:
Now, I'd like to say a few words about our integration with SonarQube. We provide the plugin that allows you to add messages found by the PVS-Studio analyzer to the SonarQube server message database. Further, you can filter messages, navigate through the code for error analysis, analyze the dynamics of the number of errors, evaluate the quality level of the project code, and so on.
To date, we are expanding the capabilities of our plugin by adding tags for diagnostics related to OWASP, AUTOSAR groups. Now the OWASP messages look like this:
Also, we classified our diagnostic rules by OWASP Top 10. The OWASP Top 10 is the ranking of the most dangerous attack vectors on web applications. Each point of this ranking has a description and examples of attack scenarios, as well as links to the rules from the OWASP ASVS Standard and the CWE classification that apply to it. You may check one of the points in the ranking.
The OWASP Top 10 includes vulnerabilities such as:
In SonarQube, it is displayed here:
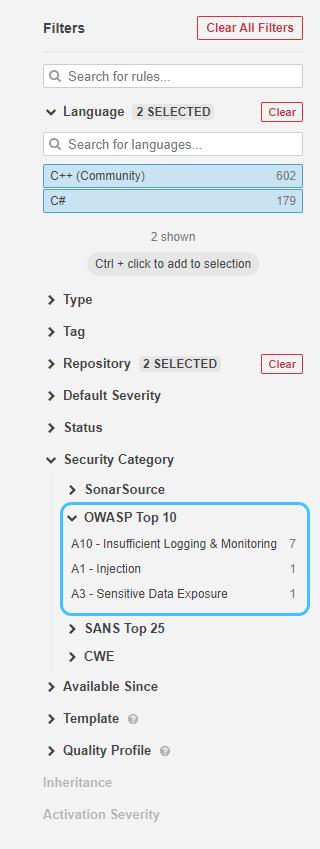
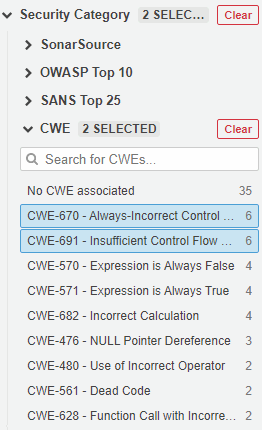
It is displayed similar to the CWE, which you can also see in the screenshot. We use a special Security Category tab for this. Here is an example of what filled CWE category looks like:
Obviously, this release was quite intense. The analyzer has received new diagnostic groups for the OWASP ASVS and AUTOSAR C++14 Coding Guidelines. In addition, analysis results contain information about the warnings' compliance with the SEI CERT Standard. The interface of our plugins for Visual Studio, JetBrains Rider, and IntelliJ IDEA has been improved to make it easier to work with analyzer messages that now have safety and security standards identifiers. Moreover, PlogConverter and SonarQube learned how to work with new diagnostic groups (OWASP, AUTOSAR). All this is just about the direction of safety and security!
It is very important. After all, the elimination of all kinds of vulnerabilities at the software development stage reduces the chance of security threats in the future. Due to this, the company won't suffer financial difficulties and ranking loss. Therefore, we try to help our users to avoid problems related to safety and security.
Be happy and keep an eye on your code. Thank you for your attention!
0