SCA (software composition analysis)
PVS-Studio recherche non seulement les faiblesses du code, mais également les composants vulnérables utilisés dans une application. Pourquoi l'analyseur fait-il cela ?
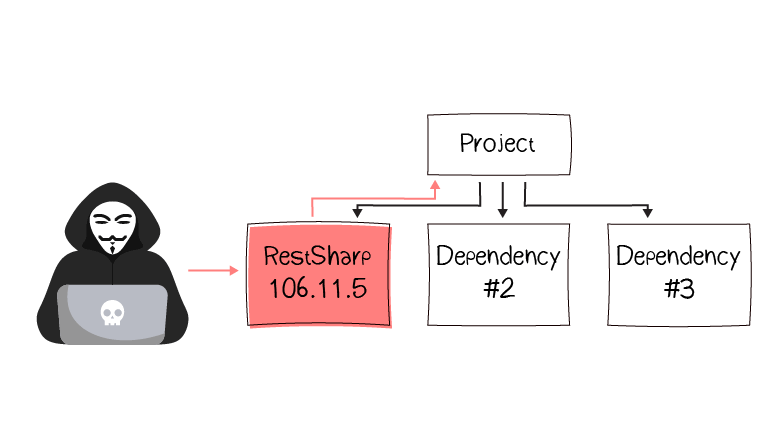
Danger dans les composants vulnérables
Les applications modernes utilisent souvent des composants tiers, dont certains présentent des faiblesses en matière de sécurité. Si une application utilise un composant vulnérable, elle peut également devenir vulnérable aux attaques malveillantes. Par conséquent, les entreprises risquent leur réputation et leurs finances.
Le Top 10 OWASP 2021 a une catégorie distincte pour l'utilisation de composants vulnérables et obsolètes : A06:2021 – Vulnerable and Outdated Components.
Est-il possible de vérifier automatiquement que l'application n'utilise pas de composants présentant des vulnérabilités connues ? Oui. Pour ce faire, des outils spécialisés effectuent l'analyse de la composition logicielle (SCA).
Les outils SCA inspectent les composants de l'application. S'ils trouvent les composants vulnérables, ils en informent les développeurs. Après cela, les développeurs peuvent mettre à jour / remplacer le composant ou protéger l'application d'autres manières.
PVS-Studio comme la solution SCA
Pour l'instant, PVS-Studio effectue l'analyse de la composition logicielle uniquement dans les projets C#. Voulez-vous avoir la même fonctionnalité pour les projets en C, C++ ou Java ? Dites-le-nous.
PVS-Studio analyse le projet et détermine les composants qu'il utilise. Si l'analyseur en trouve un vulnérable, il émet un warning. Ce warning contient le nom et la version d'un composant dangereux, la description d'une vulnérabilité et CVE-ID.
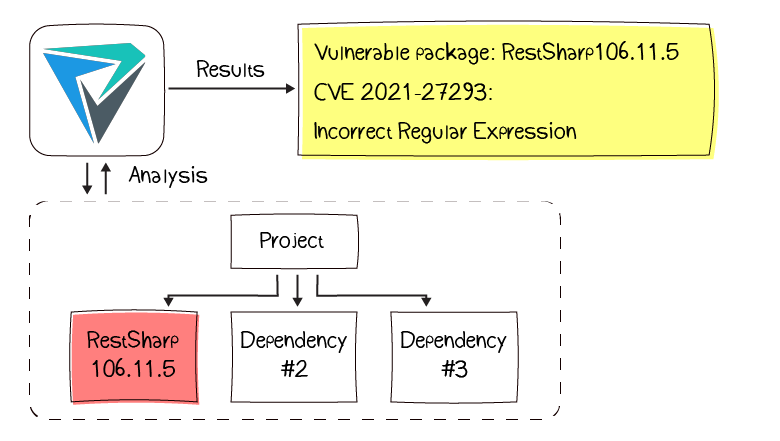
La règle de diagnostic V5625 analyse les composants logiciels. La documentation décrit comment utiliser les warnings SCA et les affiner pour un projet spécifique.
